VPN is brief for digital private network and is also pronounced as different letters.
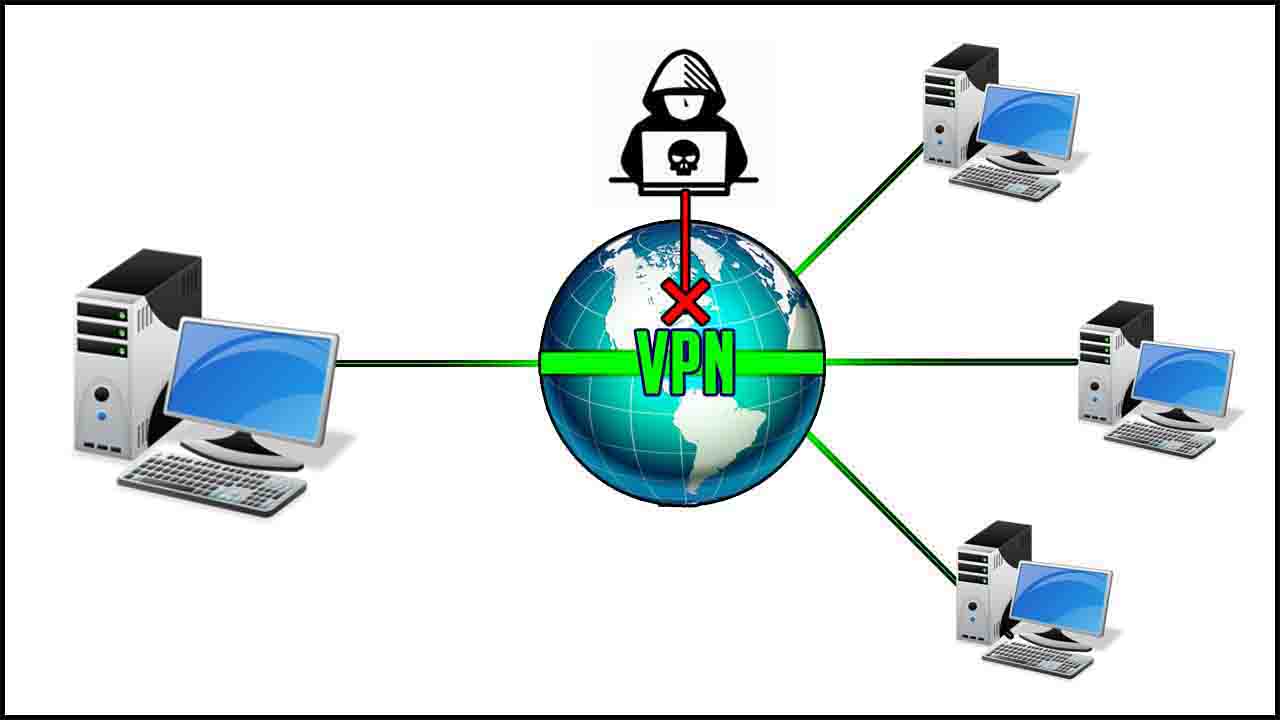
An exclusive private network (VPN) is a network that is produced using public wire connections usually the web to hook up to an exclusive network, like a company’s inner network. There are a variety of systems that permit anyone to create networks utilizing the web as the medium for carrying data. It secures the private network as these systems use encryption and other security systems to ensure that only official users can gain access to the network and this the data can’t be intercepted.
VPN Security and Privacy
A VPN was created to offers a secure, encrypted tunnel where to transfer the info between your remote control consumer and the business network. The info transmitted between your two locations via the encrypted tunnel can’t be read by other people because the machine contains several elements to secure both company’s private network and the exterior network by which the remote user connects through.
The first rung on the ladder to security is a firewall between your customer and the variety server usually, requiring the remote control user to determine an authenticated reference to the firewall. Encryption can be an important element of a secure VPN also. Encryption functions by having all data sent in one computer encrypted so that only the computer it is sending to can decrypt the info.
VPN Network Protocols
A couple of three main network protocols for use with VPN tunnels. These protocols are incompatible with one another generally. They are the following:
IPSec – A couple of protocols produced by the IETF to aid secure exchange of packets at the IP level. IPsec has been deployed broadly to use VPNs. IPsec supports two encryption modes: Transport and Tunnel.
PPTP – The Point-to-Point Tunneling Process is a technology for creating VPNs, developed by Microsoft jointly, U.S. Robotics and many remote access supplier companies, known collectively as the PPTP Community forum.
L2TP – Level Two (2) Tunneling Process is an expansion to the PPP process that permits ISPs to use Virtual Private Sites (VPNs).
Must Read- Is Public WiFi Safe
Types of VPN Services: Consumer and Corporate
Consumers use an exclusive VPN service, known as a VPN tunnel also, to safeguard their online personal information and activity. Through the use of an anonymous VPN service, a user’s Internet traffic and data remain encrypted, which prevents eavesdroppers from sniffing Internet activity. A VPN service is particularly useful when being able to access general public Wi-Fi hotspots because the general public wireless services may not be secure. Furthermore, to general public Wi-Fi security, an exclusive VPN service also provides consumers with uncensored Access to the internet and can assist in preventing data robbery and unblock websites.
Companies and organizations will typically use a virtual private network to contact secretly over a public network and send voice, data or video. Additionally, it is an outstanding option for remote personnel and organizations with global offices and partners to talk about data in an exclusive manner.
One of the most frequent types of VPNs employed by businesses is named a digital private dial-up network (VPDN). A VPDN is a user-to-LAN interconnection, where remote users need to hook up to the ongoing company LAN. A different type of VPN is often called a site-to-site VPN. Here the business would spend money on dedicated hardware to hook up multiple sites with their LAN through a public network, the Internet usually.